Mobile applications are increasingly the front door to sensitive data, and as APIs grow more complex, traditional security measures alone are no longer enough. The future of mobile API security lies in combining proven cryptographic practices with AI-powered threat detection.
Why AI-Power API Security
Static security rules can’t keep up with evolving attack patterns. Credential stuffing, API abuse, prompt injection, and behavioral anomalies require systems that learn and adapt in real time. By layering AI models into your Flutter security stack, you can detect unusual patterns, classify requests as safe or suspicious, and respond before damage is done.
Enforce HTTPS with Certificate Pinning
The foundation remains the same: encrypt everything in transit and pin certificates so a compromised certificate authority cannot issue a fraudulent cert for your domain.
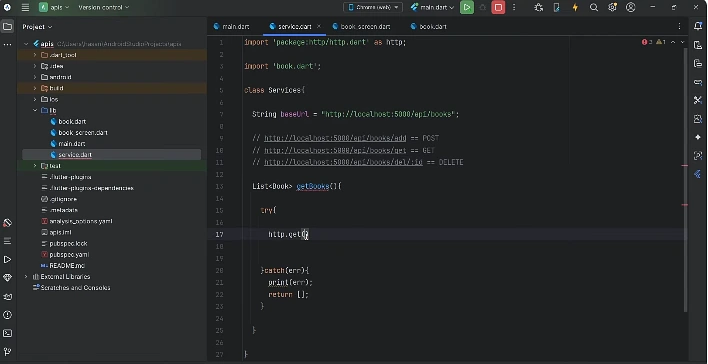
dart
import 'dart:io';
import 'package:dio/dio.dart';
import 'package:dio/io.dart';
import 'package:crypto/crypto.dart';
Dio createSecureDio() {
final dio = Dio(BaseOptions(baseUrl: 'https://api.example.com'));
dio.httpClientAdapter = IOHttpClientAdapter(
createHttpClient: () {
final client = HttpClient();
client.badCertificateCallback = (cert, host, port) {
const expectedFingerprint = 'AA:BB:CC:DD:...';
final fingerprint = sha256.convert(cert.der).toString().toUpperCase();
return fingerprint == expectedFingerprint;
};
return client;
},
);
return dio;
}Pin the Subject Public Key Info (SPKI) rather than the leaf certificate so key rotation doesn’t break your app.
Use Short Live Tokens with OAuth 2.0 and PKCE
Long-lived API keys baked into a binary are an extraction waiting to happen. Use OAuth 2.0 with PKCE, short-lived access tokens (10 to 15 minutes), and refresh tokens stored securely.
dart
class AuthInterceptor extends Interceptor {
final TokenStore store;
AuthInterceptor(this.store);
@override
void onRequest(RequestOptions options, RequestInterceptorHandler handler) async {
final token = await store.getAccessToken();
if (token != null) options.headers['Authorization'] = 'Bearer $token';
handler.next(options);
}
@override
void onError(DioException err, ErrorInterceptorHandler handler) async {
if (err.response?.statusCode == 401 && await store.refresh()) {
final retry = await Dio().fetch(err.requestOptions);
return handler.resolve(retry);
}
handler.next(err);
}
}Store Tokens in Secure Storage
Never put credentials in SharedPreferences. Use flutter_secure_storage, which delegates to iOS Keychain and Android Keystore.
dart
import 'package:flutter_secure_storage/flutter_secure_storage.dart';
final _storage = const FlutterSecureStorage(
aOptions: AndroidOptions(encryptedSharedPreferences: true),
iOptions: IOSOptions(accessibility: KeychainAccessibility.first_unlock),
);
Future<void> saveToken(String token) =>
_storage.write(key: 'access_token', value: token);AI-Powered Anomaly Detection at the Edge
Here’s where modern AI changes the game. Before forwarding a request to your backend, you can have an AI model evaluate whether the request pattern looks legitimate. This works best as a server-side gateway, but Flutter can contribute signals (device posture, interaction timing, request context) that the AI evaluates.
Here’s a Dart client calling an AI gateway that uses Claude to score request risk:
dart
class AIThreatGuard {
final Dio dio;
AIThreatGuard(this.dio);
Future<bool> isRequestSafe({
required String endpoint,
required Map<String, dynamic> context,
}) async {
final response = await dio.post(
'https://your-gateway.example.com/v1/risk-score',
data: {
'model': 'claude-sonnet-4-5',
'endpoint': endpoint,
'context': context,
},
);
final score = response.data['risk_score'] as double;
return score < 0.7;
}
}On the gateway, the AI model receives signals like request frequency, geolocation deltas, device fingerprint changes, and recent failed attempts. It returns a risk score, and your Flutter app (or middleware) decides whether to challenge the user with step-up authentication.
AI-Assisted Input Validation
LLMs are surprisingly effective at catching malformed, malicious, or prompt-injection-style payloads, especially in apps that themselves call AI services. Before sending user content to a downstream AI API, sanitize it through a classifier:
dart
Future<bool> isPromptSafe(String userInput) async {
final response = await Dio().post(
'https://your-gateway.example.com/v1/classify',
data: {
'model': 'claude-sonnet-4-5',
'task': 'detect_prompt_injection',
'input': userInput,
},
);
return response.data['classification'] == 'safe';
}This protects both your users and your AI spend by filtering jailbreak attempts before they hit a paid model.
Behavioral Biometrics and Continuous Authentication
Future-facing apps continuously authenticate based on how a user interacts with the device, including typing rhythm, touch pressure, and navigation patterns. Flutter can collect these signals via gesture detectors and ship anonymized features to a server-side model that flags session takeover attempts.
dart
class BehaviorCollector {
final List<Map<String, dynamic>> events = [];
void recordTap(Offset position, Duration sinceLastTap) {
events.add({
'type': 'tap',
'x': position.dx,
'y': position.dy,
'delta_ms': sinceLastTap.inMilliseconds,
'timestamp': DateTime.now().toIso8601String(),
});
}
Future<void> flush() async {
if (events.isEmpty) return;
await Dio().post('https://your-gateway.example.com/v1/behavior', data: events);
events.clear();
}
}The server-side model establishes a baseline per user and raises a flag when patterns drift outside their normal range.
Device Attestation with Play Integrity and App Attest
Attestation gives your backend cryptographic proof that the request is coming from a genuine, unmodified instance of your app on a non-tampered device. Combine Play Integrity (Android) and App Attest (iOS) tokens with your AI risk scoring for a powerful defense in depth.
dart
Future<String> getAttestationToken() async {
// Use packages like play_integrity_flutter or device_check
// Returns a signed token your backend verifies with Google/Apple
return await PlatformAttestation.fetchToken();
}Send this token alongside sensitive requests; the backend rejects anything missing a valid, recent attestation.
Obfuscate Builds and Strip Symbols
bash
flutter build apk --obfuscate --split-debug-info=build/symbols --releaseObfuscation won’t defeat a determined attacker, but it raises the cost of static analysis significantly.
Server-Side Remains the Real Defense
The client is always untrusted. Enforce rate limiting, per-endpoint authorization, audit logging, and key rotation server-side. AI models can monitor your API logs for emerging attack patterns and auto-generate rules for your WAF.
A future-ready Flutter security stack looks like this: TLS with SPKI pinning, OAuth 2.0 with PKCE and short-lived tokens, secure storage for credentials, AI-driven request risk scoring, prompt-injection classification for AI features, behavioral biometrics for continuous auth, device attestation for sensitive flows, and obfuscated release builds. Each layer is modest on its own, but together they raise the cost of attack dramatically.
The next wave of mobile security isn’t about building taller walls. It’s about building systems that learn, adapt, and respond, with AI as a teammate rather than a feature.