If you are a Java developer who has ever built an application using Apache HttpClient and tested it successfully on Windows, only to deploy it on a Linux server and get a confusing SSL error, you are not alone. This is one of those frustrating problems that wastes hours of debugging time because the program runs perfectly on one operating system and completely breaks on another.
The TLS SSLContext Error
When you run a Java program that uses Apache HttpClient on a Linux server, you might see this exception:
Exception in thread "main" org.apache.http.ssl.SSLInitializationException: TLS SSLContext not available
at org.apache.http.ssl.SSLContexts.createDefault(SSLContexts.java:58)
at org.apache.http.impl.client.HttpClientBuilder.build(HttpClientBuilder.java:966)
at org.apache.http.impl.client.HttpClients.createDefault(HttpClients.java:58)
at yan.javatips.closure.HttpTest2.main(HttpTest2.java:26)
Caused by: java.security.NoSuchAlgorithmException: TLS SSLContext not available
at sun.security.jca.GetInstance.getInstance(GetInstance.java:159)
at javax.net.ssl.SSLContext.getInstance(SSLContext.java:156)
at org.apache.http.ssl.SSLContexts.createDefault(SSLContexts.java:54)
... 3 moreAnd the line of code that triggers it is simply:
java
CloseableHttpClient httpclient = HttpClients.createDefault();This looks like it should work. It is the most basic way to create an HttpClient instance. But on Linux, it fails.
To Fix Error Follow These Setup
- Apache HttpClient version: 4.5.x
- JDK version: 1.8.0_101 or older builds of JDK 8
- Operating System: Linux server (Ubuntu, CentOS, Debian, RHEL)
- Works fine on: Windows with the same code and same JAR files
There are several ways to fix this problem. Start with Fix 1 and work your way down if needed.
Fix 1 – Upgrade Your JDK Version
This is the most reliable and recommended fix. JDK 1.8.0_101 is very outdated. Many SSL and TLS bugs were fixed in later builds of JDK 8. Upgrading to a newer version resolves the issue in most cases without any code changes.
Run the following commands on your Linux server:
On Ubuntu or Debian:
bash
sudo apt-get update
sudo apt-get install openjdk-8-jdkOn CentOS or RHEL:
bash
sudo yum install java-1.8.0-openjdk-develAfter installing, verify the version:
bash
java -versionYou should now see a newer build such as 1.8.0_312 or higher. Run your program again and the error should be gone.
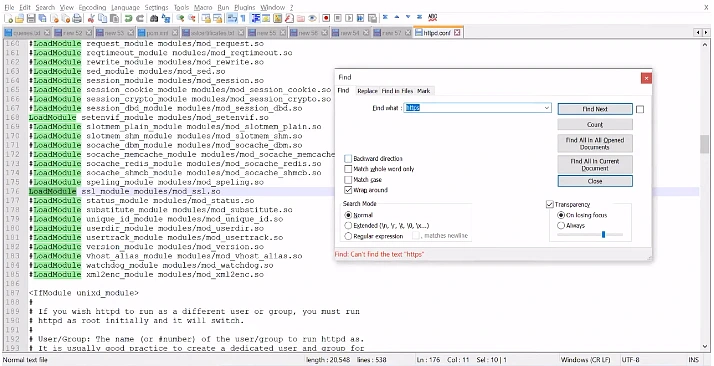
Fix 2 – Check and Repair the java.security File
If upgrading the JDK is not an option, the next thing to check is the java.security file. This file tells the JVM which security providers are available. If the TLS provider is missing or commented out, SSL will not work.
Open the file with this command:
bash
sudo nano $JAVA_HOME/jre/lib/security/java.securityFind the section that lists security providers and make sure these lines are present and not commented out:
security.provider.1=sun.security.provider.Sun
security.provider.2=sun.security.rsa.SunRsaSign
security.provider.3=sun.security.ec.SunEC
security.provider.4=com.sun.net.ssl.internal.ssl.Provider
security.provider.5=com.sun.crypto.provider.SunJCEIf any of these lines are missing or have a # at the beginning, restore them, save the file, and restart your application.
Fix 3 – Fix the Code Directly Without Changing the Server
If you cannot change the server environment at all, you can work around the problem directly in your Java code. Instead of using HttpClients.createDefault(), you manually initialize the SSLContext and build the client yourself. This gives you full control over how SSL is set up.
Replace your original line:
java
CloseableHttpClient httpclient = HttpClients.createDefault();With this:
java
import org.apache.http.impl.client.CloseableHttpClient;
import org.apache.http.impl.client.HttpClientBuilder;
import org.apache.http.conn.ssl.NoopHostnameVerifier;
import javax.net.ssl.SSLContext;
SSLContext sslContext = SSLContext.getInstance("TLSv1.2");
sslContext.init(null, null, new java.security.SecureRandom());
CloseableHttpClient httpclient = HttpClientBuilder.create()
.setSSLContext(sslContext)
.setSSLHostnameVerifier(NoopHostnameVerifier.INSTANCE)
.build();By explicitly requesting "TLSv1.2" instead of relying on the default "TLS" string, you bypass the initialization problem that causes the error.
Fix 4 – Install Missing SSL Packages on Linux
On Ubuntu or Debian:
bash
sudo apt-get install ca-certificates openssl libssl-devOn CentOS or RHEL:
bash
sudo yum install ca-certificates opensslAfter installing, update the CA certificates:
bash
sudo update-ca-certificatesThen run your program again.
Fix 5 – Relink the cacerts File
Sometimes the cacerts file inside the JDK becomes broken or unlinked from the system certificates on Linux. You can fix this by relinking it:
bash
sudo ln -sf /etc/ssl/certs/java/cacerts $JAVA_HOME/jre/lib/security/cacertsRestart your application after running this command.
Quick Diagnosis Checklist
Before applying any fix, run through this checklist on your Linux server to quickly identify what is wrong:
bash
# Check Java version
java -version
# Check JAVA_HOME is set
echo $JAVA_HOME
# Check if security folder exists
ls $JAVA_HOME/jre/lib/security/
# Check if cacerts file exists
ls -la $JAVA_HOME/jre/lib/security/cacerts
# Check SSL availability
java -XshowSettings:all -version 2>&1 | grep -i sslSummary
| Fix | When to Use |
|---|---|
| Upgrade JDK | Best first step, works in most cases |
Fix java.security file | When providers are disabled on the server |
Fix code with TLSv1.2 | When you cannot change the server |
| Install SSL packages | On minimal Linux installations |
Relink cacerts | When certificates are broken or missing |